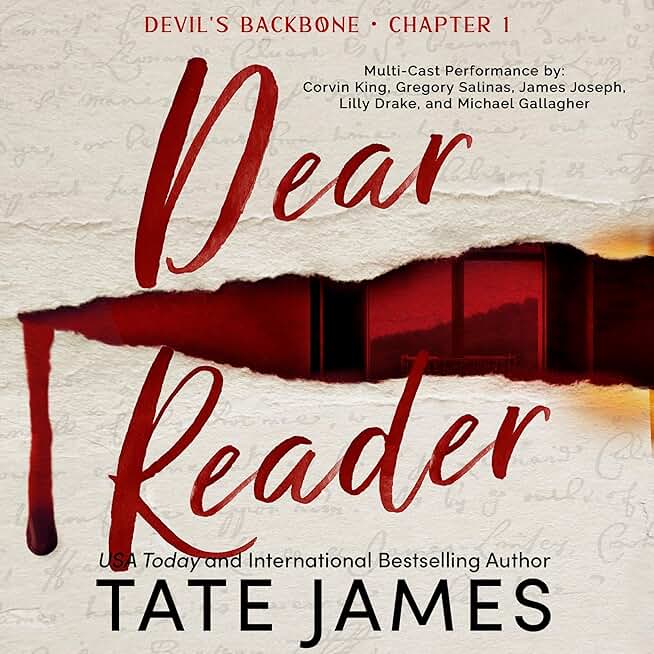
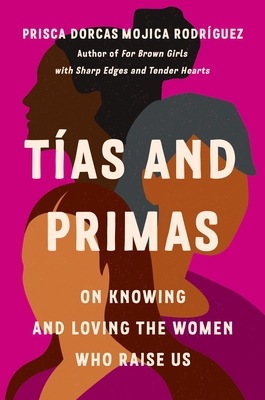
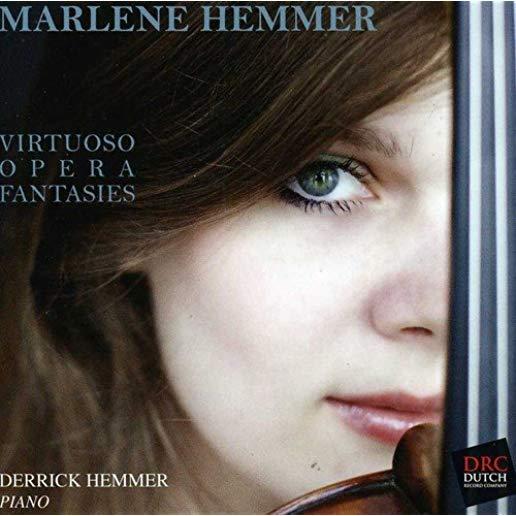
Item is not available
member goods
No member items were found under this heading.
Return Policy
All sales are final
Shipping
No special shipping considerations available.
Shipping fees determined at checkout.